I recently sent my ASUS ROG STRIX GeForce® GTX 1080 TI 11GB OC in for an RMA after my games started crashing within a few minutes; looking at the Event Viewer I found error messages indicating the Nvidia drivers were resetting (Display driver nvlddmkm stopped responding and has successfully recovered). To date I have only had one previous experience with ASUS RMA support; back in 2011 a friend of mine overseas gave me his RAMPAGE GENE III that was dead. I was able to RMA it with no issues and used it for an i7-950 build.
Here is the timeline of events:
- Monday July 22 – I contact ASUS Support through the website and state I have tried troubleshooting by reinstalling drivers, reinstalling Windows 10, trying different PCIE slots and a different system.
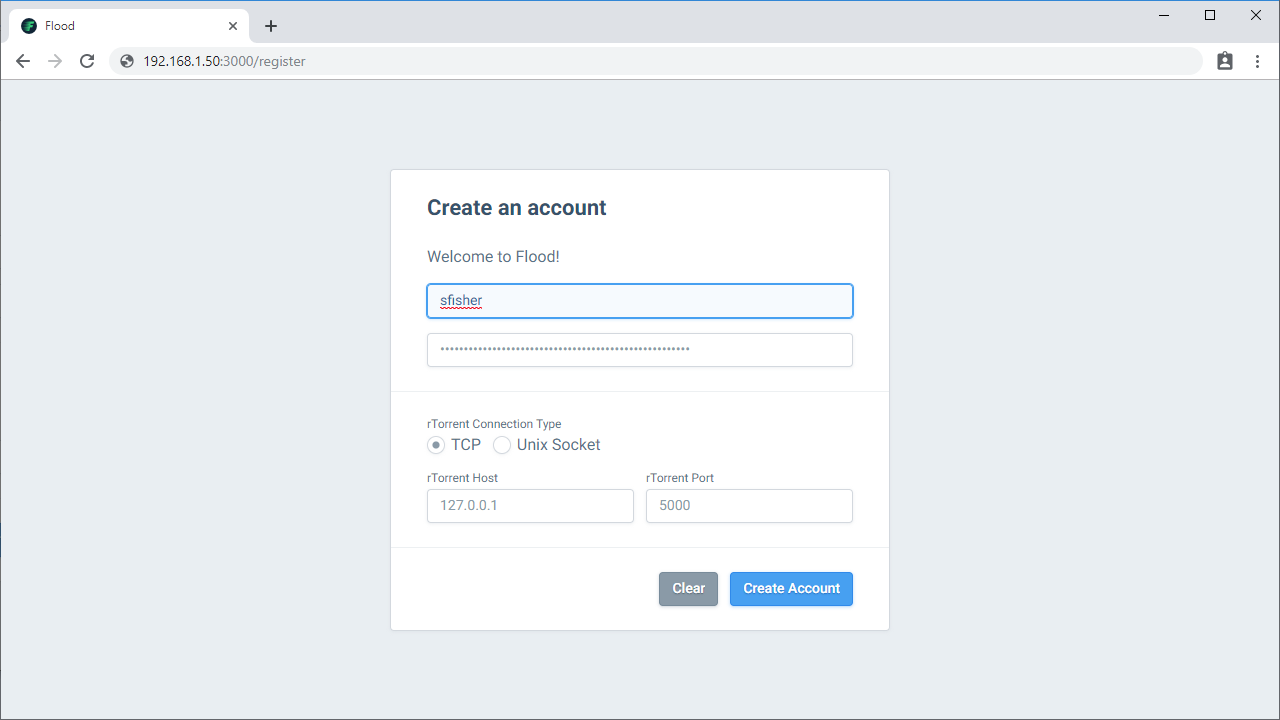
- Tuesday July 23 – I receive a reply from an ASUS Support Agent. Based on my initial message, they direct me to create an Online RMA by visiting https://www.asus.com/us/support/Article/818 (looks like I could have saved a step by going directly to this page). I fill out the Online RMA request that morning and let the Agent know I have done so. They reply back in the afternoon stating the Online RMA was not successfully pushed through and offer to process it manually.
- Wednesday July 24 – The Agent confirms my RMA has been processed; I receive an RMA Number and instructions on how to ship my 1080 Ti. I package the 1080 Ti and drop it off at USPS in the afternoon (I did not purchase the label from ASUS). It is expected to arrive at the RMA facility by Friday July 26.
- Friday July 26 – The USPS tracking number reports there is a delay.
- Monday July 29 – I check the tracking number again and the 1080 Ti has been delivered successfully.
- Tuesday July 30 – I visit the ASUS Check Repair Status page and it shows ASUS has received my 1080 Ti.
- Wednesday July 31 – I visit the Status page again and it is in the testing phase.
- Thursday August 1 – I receive a notification from the Fedex Delivery Manager that I have a package coming from ASUSTEK. I look at the Status page and it confirms my repair has been completed. There is no mention of what the replacement card is so I assume it is another 1080 Ti.
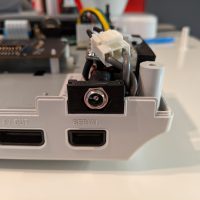
- Wednesday August 7 – I receive the package from ASUS. I open it to find a ROG Strix GeForce RTX™ 2080 OC.
It took 16 days from first contact to when I received my replacement graphics card. Potentially this could have been faster if USPS delivered my 1080 Ti on Friday instead of Monday and if I had created the Online RMA directly rather than contacting support first. The replacement took just under a week to be delivered; it was ground shipped from Jeffersonville, Indiana and I live on the opposite side of the US (West Coast).
Overall I would consider this experience a positive one; much better than the time I had to RMA Sapphire 290s repeatedly. The 2080 is a minor upgrade over the 1080 Ti according to TechPowerUp’s review. I have been using ASUS graphic cards since purchasing the ASUS STRIX GEFORCE® GTX 980 Ti back in 2016. After that came the 1080 Ti and now the 2080 replacement. I also have the ROG Strix GeForce RTX™ 2080 Ti OC which I bought after sending in my 1080 Ti (I used this whole ordeal as an excuse to upgrade). If you are having trouble deciding which brand of graphics card to buy, consider differentiating them by their customer support and where their RMA center is. For example, Gigabyte’s RMA facility is located in City of Industry, CA which is a lot closer to me than Indiana.